Torrents: the good, the bad, and the ugly
Tags:
A number of leading torrent websites have gone offline recently, drawing attention again to the use of torrents to share copyrighted material. But the absence of these sites doesn’t mean torrents have stopped. Torrenting is a peer-to-peer technology that doesn’t have a single point of failure. Just because some sites have gone down, doesn’t mean you don’t have to care about torrents on your network. In this post, I want to look at the good, the bad, and the ugly of torrents.
Torrent technology is great for sharing large files — it’s easy, fast, and resilient. This has made it a popular means of quickly sharing Linux distributions and other large open-source systems. For the same reasons, some companies are experimenting with torrents for software distribution. But it’s not just legitimate software that’s being shared; there are companies using the technology to share copyright-free media content such as independent movies. All of this is perfectly legal and good.
The bad part comes with the sharing of copyrighted content. It’s no secret that large volumes of copyrighted materials are being shared via torrents. If a company’s employees are using the corporate network to torrent, this is a misappropriation of a company’s computing resources, but worse than that is the legal risk. Copyright holders are understandably keen to protect their revenue, so copyright alerting systems exist to locate IP addresses torrenting copyrighted content. Once these IP addresses are tracked back to companies or individuals, copyright enforcement agencies send legal letters. For a company, complying with the terms of these legal letters means hunting down content and removing it from the corporate network. At best, it’s a nuisance and diversion of IT resources.
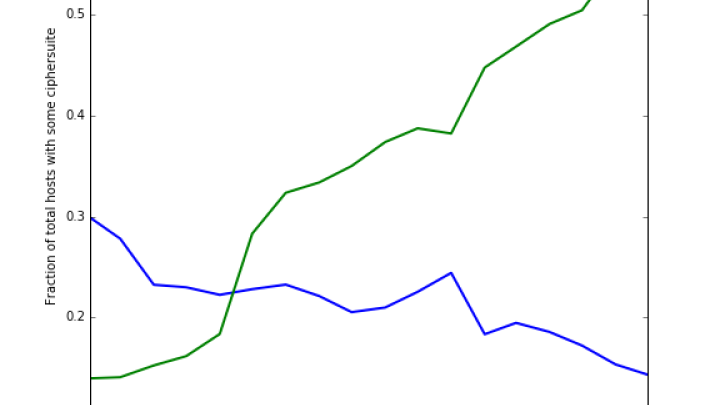
The really ugly part comes from the risk of running torrented executables on the corporate network. Bitsight found a very high malware infection rate for torrented applications (43%) and games (39%). If torrents have a high rate of malware infection, you’d expect to see companies that torrent more have more botnets. Bitsight looked at this too. Obviously, the larger a company, the more torrents you would expect to see, so this must be factored into the analysis. Here’s the result.

The vertical axis is the monthly count of botnet infections per employee, the horizontal axis is the monthly count of torrents per employee. The bottom line is that companies that have more torrenting on their network have more botnets. It’s a clear result.
Creating a policy for staff torrenting on your network can be a balance. On one hand, you may want to allow staff to torrent legitimate content like Linux distributions, but on the other you may wish to block some content to avoid legal and network risks. There is one point you should bear in mind; no matter how many torrent websites are taken down, the risks of peer-to-peer torrenting still exist.
Now that the shift to remote work and bring-your-own-device policies have exposed organizations to more risk, cybersecurity teams are monitoring for and responding to threats introduced from employee's home network devices. Bitsight's Attack Surface Analytics reporting can help you scan and secure your third party networks for potential exposure.



