Third-party Continuous Monitoring helps you decide what needs attention first. Bitsight Threat Intelligence reinforces and refines those priorities with real-world threat context, so you can make faster, more informed decisions about what to do next.
Bitsight Threat Intelligence
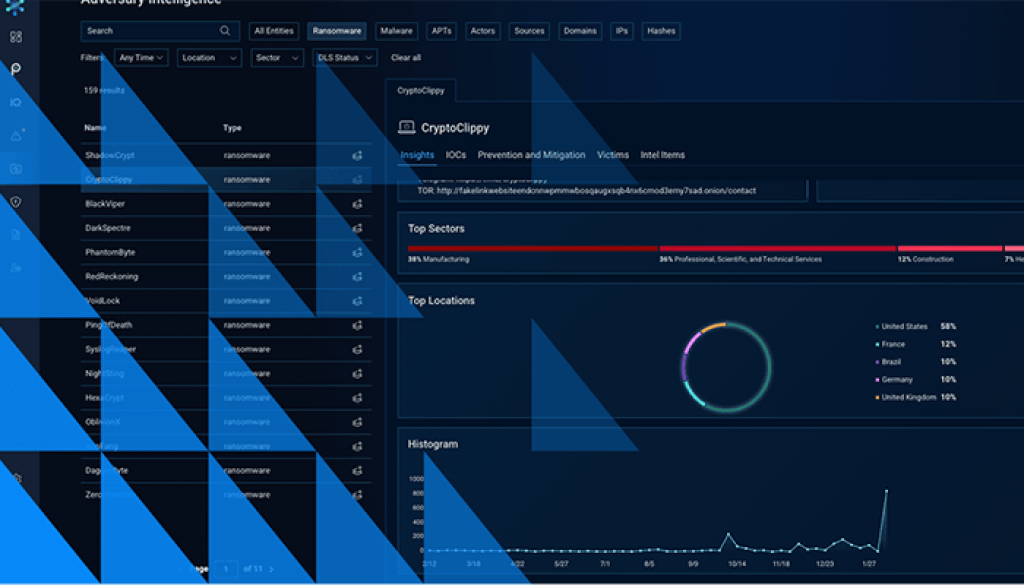
See the threat activity behind what you prioritize
How Threat Intelligence helps your team act on priorities
When it may be time to explore Threat Intelligence
Bitsight Threat Intelligence may be worth a closer look if your team needs to:
- Understand whether a vulnerability is tied to real-world exploit activity, not just severity
- Identify exposed credentials or access-for-sale activity tied to your users or domains
- Track threat actors or campaigns relevant to your industry or region
- Give SOC or threat-focused teams better information to investigate and respond faster
- Cut through disconnected feeds and low-signal alerts
See how threat intelligence can strengthen your resilience strategy
If your team needs more context behind the risks you already prioritize in Continuous Monitoring, Bitsight Threat Intelligence can help you investigate more deeply, align teams sooner, and focus on the threats most likely to matter.
Learn how Bitsight Threat Intelligence can support your team.
