Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Bitsight and Google collaborate to reveal global cybersecurity performance

Bitsight and Google collaborate to reveal global cybersecurity performance
This joint study between Bitsight and Google arms organizations with actionable insights, providing the current status of global cybersecurity performance by analyzing nearly 100,000 global organizations across 16 cybersecurity controls and nine industries amid heightened stakeholder demands on cybersecurity strategy.

Although Bitsight cannot influence the risk appetite of an insurance company, we can help you understand your cyber hygiene while proving to insurers that you are actively invested in your security posture, which influences the coverage decision.

Key risk indicators (KRIs) can help monitor and control cyber risk. But what KRIs should you focus on?

The Bitsight Badge enables an organization to prove their focus on security, increase transparency, and showcase the hard work they put into enhancing security performance.

What is a board cybersecurity committee? Learn why it’s more critical than ever and how your organization can establish one.
What is a botnet? A botnet is a collection of networked devices that are infected by malware and hijacked to carry out scams and data breaches.

Investors are worried about cybersecurity—and for good reason. Yet despite growing concerns and the criticality of the issue, the dialogue between companies and investors need significant improvement. Here's why.

In 2021, ransomware attacks on government agencies globally increased by 1,885% over 2020 attacks, and the trends are continuing so far in 2022. Learn how to protect your organization from ransomware with three best practices.
Malware can gain entry to your network in many ways. Once malware has penetrated a network, threat actors can use it to steal information, encrypt systems, spy on users, and remove files. Learn how to prevent dangerous malware.
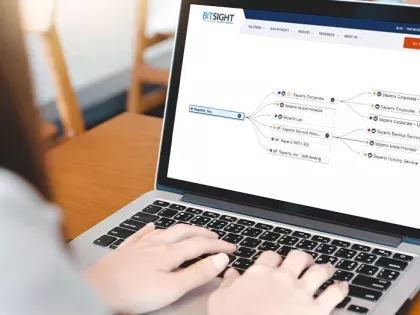
The Bitsight Ratings Tree gives you insight into the different portions of your business to identify gaps and weaknesses in your program performance.

Learn about the four pillars of cyber preparedness and why it’s everyone’s responsibility to get involved.

To improve cyber resilience, you must first measure it. Learn the 4 metrics to track to gain insights into your cybersecurity posture.

Ransomware isn’t going away; security leaders need to get inside the brain of ransomware sleuths and learn how attacks develop to better identify early indicators of ransomware in their network. Read on to learn how ransomware attacks happen.

Explore actionable attack surface reduction examples that can reduce risk across your expanding digital environment.

Learn what you can do to defend against cyber attacks and achieve a state of cyber resilience.

The attack surface encompasses the digital assets that a hacker can exploit. An attack vector is the method they use to breach the attack surface.