Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Bitsight and Google collaborate to reveal global cybersecurity performance

Bitsight and Google collaborate to reveal global cybersecurity performance
This joint study between Bitsight and Google arms organizations with actionable insights, providing the current status of global cybersecurity performance by analyzing nearly 100,000 global organizations across 16 cybersecurity controls and nine industries amid heightened stakeholder demands on cybersecurity strategy.

These are the basic steps you should take to develop an effective cyber risk management strategy.

Ransomware is getting more sophisticated, and 1 in 4 breaches involve ransomware. Bitsight analyzed hundreds of ransomware events to estimate the relative probability that an organization will experience a ransomware event. Four areas bubble to the top.

When it comes to improving cybersecurity at your organization, there are some fixes that you can undertake with very little preparation. More robust remediation efforts, however, usually start with a cybersecurity risk assessment.

We look at five ways you can reduce cyber threats without putting additional pressure on stretched resources.

Let’s look at how you can establish a cybersecurity baseline that works for your unique risks, industry, and business.

Data exfiltration is the unauthorized transfer of data from a host device, such as an application, database, or server. Here’s how you can prevent it.

What is a cyber resilience framework? Learn how your organization can better prepare for, respond to, and recover from a cyber attack.

A majority of boards now see cyber risk as business risk, so they’re asking hard questions around risk and exposure. Security leaders must have processes in place to inform and educate executives, boards, and stakeholders as to the security posture of the organization as well as the postures of important third parties.

People’s perception of your cyber risk will outweigh its actual performance. And when trust in cybersecurity takes a nosedive, it can make a big dent in your financials. Learn how to prove protection and build trust with three key stakeholder groups.

As the world adjusts to more working from home, IT teams worked overtime to enable remote access for millions of employees.

To be effective as a security leader you must find ways to help your SOC teams improve cyber vulnerability awareness and time to remediate. Let’s explore how.

Learn how to scale your cybersecurity program with automation, continuous monitoring, and powerful data insights.

How cybersecurity leaders can manage an expanding attack surface, increasing vulnerabilities, and growing demands from stakeholders.

Imagine you've alerted your IT team to a critical infrastructure error plaguing your network. You ask them to drop their current work and focus on immediate remediation of this detected vulnerability. After further investigation, however, it is found to be a false positive.
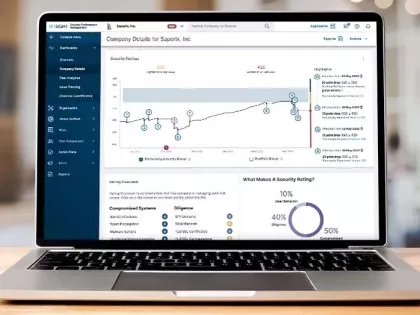
Security ratings, or cyber security ratings, are a data-driven, objective and dynamic measurement of an organization’s security performance. Thousands of organizations around the world use Bitsight Security Ratings as a tool to address a variety of critical, interconnected internal and external use cases at scale in order to enable more effective decision making throughout the global business ecosystem.